Digital Identity, use Verifiable Credentials with Blockchain
A solution that uses blockchain-based underpinnings and cryptographic keys, to ensure that YOU are in control of your own identity online. Owning your identity is more relevant than ever. In the digital environment, it’s hard to retain ownership of your identity once you’ve shared it. Every time you give away personal information in exchange for a service — like bank account numbers, proof of education, or even employment, it’s now in the custody of those different institutions. You no longer control the data associated with them, and you can’t take it back.

Verifiable Credentials is one of the most exciting and transformative areas of innovation. Verifiable Credentials and Decentralized Identifiers help you share your verifiable credentials without giving up your privacy. No one company or institution can control or store your information centrally — you can revoke your verifiable credentials at any time.
Joy Chik, Microsoft’s Identity CVP, joins Jeremy Chapman to show you how it works and gives you the key steps to get up and running.
QUICK LINKS:
00:07 — New solution: Verifiable Credentials
01:39 — What is it, and how do things change?
02:16 — See how it all works
06:29 — Blockchain-based
08:04 — Get it up and running
13:26 — Where else are Verifiable Credentials applied?
14:08 — Links to learn more
Link References:
To learn more and get all of the tutorials, go to https://aka.ms/DIDForDevs.
Download the Verifiable Credentials SDK and create your own DID at https://aka.ms/VCSDK.
Keep up to date with our Decentralized Identity blog at https://aka.ms/IdentityBlog/DID.
Unfamiliar with Microsoft Mechanics?
We are Microsoft’s official video series for IT. You can watch and share valuable content and demos of current and upcoming tech from the people who build it at Microsoft.
- Subscribe to our YouTube: https://www.youtube.com/c/MicrosoftMechanicsSeries?sub_confirmation=1
- Follow us on Twitter: https://twitter.com/MSFTMechanics Follow us on LinkedIn: https://www.linkedin.com/company/microsoft-mechanics/
- Follow us on Facebook: https://facebook.com/microsoftmechanics/
Video Transcript:
Hello, and welcome to a special edition of Microsoft Mechanics with Microsoft’s Identity CVP Joy Chik, to cover a brand new solution called Verifiable Credentials that uses blockchain-based underpinnings and cryptographic keys to ensure that you’re in control of your own identity online. So, Joy, it’s been a while. Welcome back to Microsoft Mechanics. It’s great to have you back and speaking about one of our favorite topics: identity.
- Thank you. It is great to be back.
- So, this whole topic of owning your own identity is more relevant than ever. Now, we’ve all heard stories or maybe even experienced times where our identities may have been compromised or even stolen, yet in the digital environment, it’s hard to retain ownership of your identity once you’ve shared it.
- Right, and that problem compounds every time you give away personal information in exchange for a service, like bank account numbers and a proof of education, or even an employment, and once you give it away, you can’t take it back. It is part of your growing digital footprint. Think about all of the services that you sign into every day to enable day-to-day transactions, or your school ID, or employer-issued IDs. Once you share your information, it is now in the custody of those different institutions. It is hard to keep track of the different accounts. You can no longer control the data associate with them, and you can’t take them back.
- Okay, so how do things change, then, with Verifiable Credentials?
- This is one of the most exciting and transformative areas of innovation that we are contributing to at Microsoft. A verifiable credential is a piece of information that a third party can validate digitally. In partnership with the open standards community, we are implementing an approach that’s based on W3C standards for verifiable credentials and decentralized identifiers to help you share your verifiable credentials without giving up your privacy. No one company or institution can control or store your information centrally. You can revoke your verifiable credentials at any time.
- Okay, so how does it all work?
- Let me explain with a real-world example. There are three parties in this chain of trust: the issuer, the subject, and a verifier. The issuer creates the verifiable credential. This can be an organization or entity that asserts information about you, like your employer or university. In this case, the issuer is the United States Department of Defense. The Navy MilGears program is piloting a solution to digitally issue verifiable credentials to each service member. They are the subjects who can now easily prove their skills to an accredited institution, what we call the verifier. This way, the subject can present credentials issued directly from the source, and as a result, hopefully accelerate their career.
- Okay, so can we see it?
- Yes, let me show you this in action. So, here, MilGears has made its verifiable credential service available to service members through their portal. To retrieve credentials as a service member, I just need to securely authenticate, and once I’m signed in, I can access my service history, training, education, and credentials. I’m going to pick up where I left off. Now, if I scroll down, you’ll see the individual digital record that the DOD is attesting in the verifiable credential; in this case, my high school graduation status. To accept and activate the credential as a service member, I can scan the QR code with a supported authenticator app, and in this case, it’s Microsoft Authenticator. This stores a unique private key. Although you cannot see it on my screen, it has signed me in with biometric proof. Scanning the QR code stores the verifiable credential in the digital wallet on my device. Next, to complete my university application as a service member, I need to submit my military credentials. On a participating university site, in this case Trident, I just need to sign in with my usual username and a password, and in my case, I know I need to get my high school diploma verified, so I will click there. I will click here to verify, and that pops up a QR code. So, I will scan that, and if I’m there, I’m prompted to approve the request on my phone by tapping Accept, and once I approve it, the university can now access my verifiable credentials within seconds, and the beauty of this approach is your authenticator app keeps a record of every time you share your credentials.
- Okay, so for this process to work, clearly, there must be incentives, then, for each party.
- Yes, everyone benefits in this scenario. The issuer, in this case MilGears, gains a more efficient process by verifying service member information. They also don’t bear the risk of storing sensitive personal data. That data stays with the subject. The verifier, in this case the university, can trust the subject’s information because it comes directly from the issuing source. So, they save the time and the cost on background checks. And as a subject or service member, I have control over my information and can revoke access to it at any time. As long as issuers and the verifiers participating in this approach, you can prove anything about yourself while retaining full ownership of your digital footprint.
- And that’s great because for this approach to take off, there has to be a high level of convenience really for all parties involved, but what’s enabling the issuance and verification processes to work?
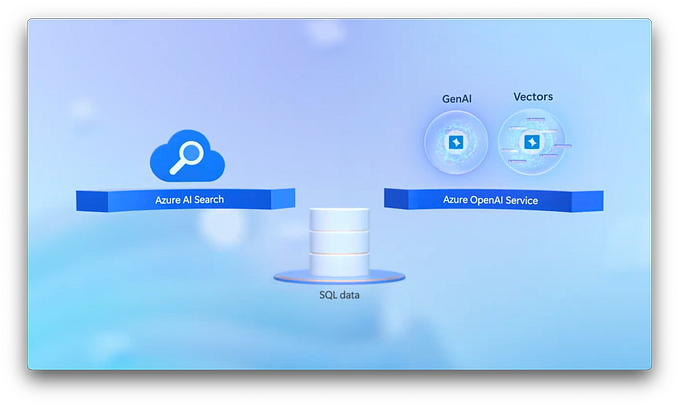
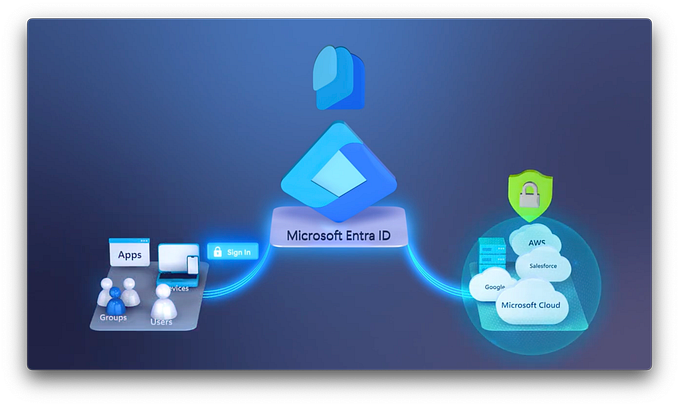
- Under the covers, we’re using a blockchain-based distributed ledger with crypto keys as an intermediary. To participate in this process in Microsoft implementation, the issuer uses Azure AD with Azure Key Vault to register a key pair to the blockchain. The verifier does this using the Verifiable Credential SDK. During this process, each party gets a unique decentralized identifier, or DID, that gets written to the ledger along with their associated public key. The subject uses the authenticator app to generate a crypto key pair stored on their device. Once they accept that first credential, it is registered on the blockchain with the DID that is also associated with their public key.
- Okay, so this then allows all three entities to be looked up in a trusted manner, all while protecting their privacy.
- That’s right, so for example, when the service member approved the request for verification by scanning the QR code, it’s passed the credentials to the university. The university were then able to verify the service member’s DID and the issuer’s DID by looking up the public keys in the distributed ledger.
- And all of this happens in just a few seconds. So, it’s very efficient and establishes the chain of trust across you, the issuer, and the verifier. But this is Mechanics, so we’re gonna show you the key steps to get all this up and running, starting with the issuer. Now, while this is based on open standards and could run anywhere from Microsoft’s implementation, you’ll need a couple of services in place as the issuer. First, an Azure subscription, and also Azure Active Directory Premium or trial. You’ll need to enable your Azure AD tenant for verifiable credentials, and this assigns you with the decentralized identifier, DID, and also equips your tenant with a service so that you can actually issue credentials, and you can learn more about all of this, by the way, aka.ms/DIDForDevs, and also, you’ll need an Azure Key Vault and storage account.
- That’s right, and then you take just three steps to configure and issue verifiable credentials. The first step is to connect your tenant to the distribute ledger. Here in the Azure Key Vault, you will generate and manage a pair level crypto keys, one private and one public. Azure AD then publishes the DID and then the public key to the distributed ledger, to manage signing, recovery, and updates for your DID.
- Now, Azure AD customers can securely manage their keys to sign the verifiable credentials themselves.
- That’s right. The second step is to configure the properties of your verifiable credential. To do this, you create a rules file, which is a simple JSON file that defines the properties for the verifiable credentials being issued. On the left are credential details from the Azure portal, and on the right is VS Code, with the two key files we need to create, one for rules and one for the card display. Let’s start with the rules file. You will see that it includes the credential issuer’s address that’s mapped to their domain address. Much like traditional identity tokens, an issuer can choose to set an expiration for the credential expressed in seconds. Next, it calls out the verifiable credential type and ties that to learning record schema. So, applications can decipher the transcript and then map it to their own business process, and then finally, the issuer can declare what the user must present to receive such a credential. This can be self-attested information from filling out a digital form, for example. It can be one or more ID tokens, which can come from a traditional identity system like Facebook, Google, or a work account, or even verifiable credentials from some other issuers.
- And I noticed that this one was actually branded as MilGears, so how did you do that?
- For that, let’s take a look at our card display file to configure the look and the feel for the credential. As I mentioned before, verifiable credentials issued to you look like just the cards in your Microsoft Authenticator wallet. Issuers can customize them using the card configuration JSON file that you can see here. We’re able to specify the card’s color, icon, and the text strings to match the MilGears look and feel, and I can use other fields to let users know the purpose of the card, its attributes, and much more.
- Okay, so that’s the issuer’s role, but let’s switch gears to the verifier. What do they need to do?
- If you are the verifier, you still need to do a few things for this to work. To get started, you need to download the Verifiable Credentials SDK, and then create your own DID. You can find that at aka.ms/VCSDK. You also need to create a QR code or deep link and then publish to your website or include it in an email to trigger the verification process. This QR code or deep link will trigger a process that you can create using the Verifiable Credential SDK. Let’s look at the code that is behind the request that our QR code links to. This is a presentation request to initiate the request for a subject’s credential. The verifier receives a response that they can trust by verifying three things. Let’s take a closer look at the response file, and you will see. Proof of presentation. You verify this by matching the signature of the presenter with the DID of the subject in the credential. Proof of authenticity. You also verify the signature of the presenter by looking up their public key on the ledger. Proof of issuance. You verify the signature of the issuer by looking up their public key on the ledger.
- All right, and just to be clear, for the user, it’s really easy. They’re just using the Authenticator app.
- Yes, that’s right. Once the subject is issued the verifiable credential, it is available as another card in their wallet, and they can use to prove information about themselves.
- Right, and just like that, the circle of trust with this decentralized identity approach is established, and I like that you broke out of the conceptual realm to really show how this gets implemented with the real example of using the Department of Defense, but where else do you see verifiable credentials being used? What’s next?
- Well, starting with skills verification, beyond what I just showed you, imagine even broader applications like presenting verifiable credentials on your LinkedIn profile. How cool would that be to help speed up the hiring and onboarding process?
- Very cool. I can see this really speeding up the job application process.
- And of course, beyond skills, there’s a broad range of scenarios where verifiable credentials can create more efficiency. Think of industries like healthcare and finance, where both privacy and the validating information that people share is just so important.
- Okay, so for the people that are watching this that wanna try it out, where they go to learn more?
- To get started, you can go to aka.ms/DIDForDevs to get all of the tutorials. We’re also looking for customers with a skills verification use case to join our private preview, and our Decentralized Identity blog at aka.ms/IdentityBlog/DID is a great way to keep up-to-date on our progress in this space.
- Thanks, Joy, for being on the show today. It’s always fantastic to have you on, and thank you so much for joining us today. This is a popular topic, and we hope that we’ve answered all of your questions and made it real for you, and don’t forget to subscribe to Microsoft Mechanics and keep watching the latest updates in this area and much more. Thanks for watching. We’ll see you next time.